
Microsoft’s September Patch Tuesday update arrived on schedule late on 13 September, and this month contained five critical common vulnerabilities and exposures (CVEs) and one actively exploited zero-day, among a total of... Read more »

The death last week of Queen Elizabeth II at the age of 96, following a 70-year reign, has drawn global attention and may yet draw the focus of cyber criminal elements exploiting... Read more »

The UK’s Financial Conduct Authority (FCA) has revealed evidence of a dramatic and ongoing surge in the number of distributed denial of service (DDoS) attacks against the financial sector, with a quarter... Read more »
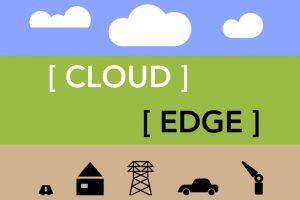
Processing and data storage happen on edge systems over the cloud. But network constraints may be the best way to distinguish edge from cloud. Illustration: Andy Wolber/TechRepublic Must-read big data coverage At... Read more »

By What is data masking? Data masking is a method of creating a structurally similar but inauthentic version of an organization’s data that can be used for purposes such as software testing... Read more »

The banking giant announced the acquisition of the cloud company on Monday. Image: Lewis Tse Pui Lung/Adobe Stock The digital transformation that hit financial institutions globally after the COVID-19 has continued unabated.... Read more »

Riverbed has released Alluvio IQ, a SaaS unified observability solution that promises to simplify digital experience management. Learn more here. Image: peopleimages.com/Adobe Stock Today, Riverbed released Alluvio IQ, a cloud-native SaaS solution... Read more »
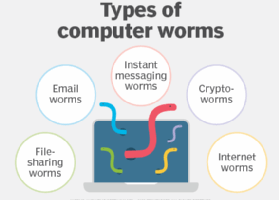
What is a computer worm? A computer worm is a type of malware whose primary function is to self-replicate and infect other computers while remaining active on infected systems. A computer worm... Read more »

It takes an average of just three steps for a threat actor to infiltrate a target cloud environment and get to its “crown jewel” assets, and as a result, vast numbers of... Read more »

Researchers at Secureworks’ Counter Threat Unit (CTU) have warned of a new and potentially serious vulnerability affecting the pass-through authentication (PTA) hybrid identity authentication method used in Azure Active Directory (AD). PTA... Read more »
